
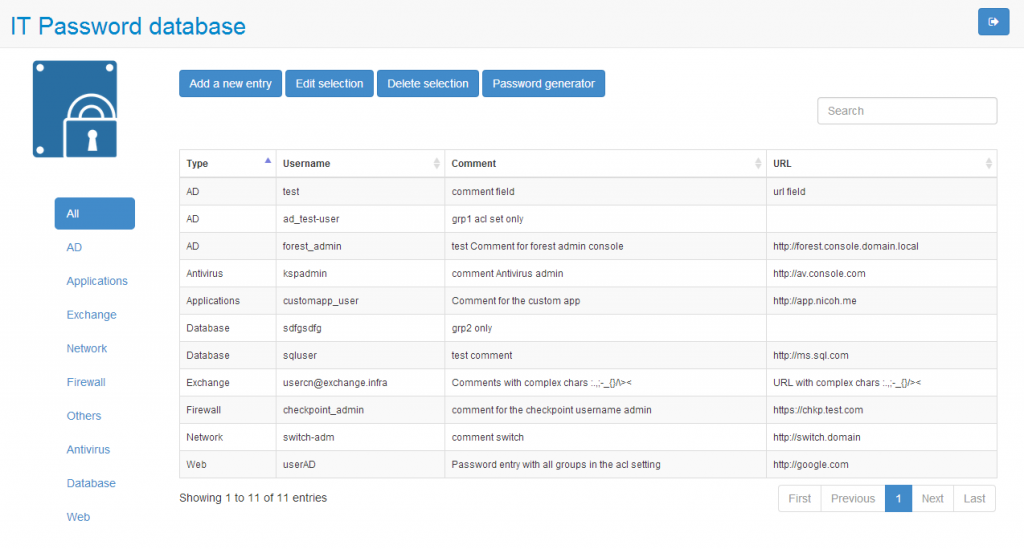
This project is a secure password repository to store and manage them based on an Apache web server, PHP and MySQL
You can test from now the demo here
The following users/passwords are defined :
- user1/pwd1
- user2/pwd2
- user3/pwd3
Features
- Active Directory authentication using adLDAP PHP module
- Multiple Active Directory group support
- Real web interface login and logout
- Bootstrap design
- Datatables javascript library layout
- Unique configuration file
- Encrypted password in the database
- Encrypted communication between the browser and the database
- Works on Chrome and Firefox
Requirements
- Apache configured with SSL support
- MySQL
Installation
The installation is quite simple :
- Create a new vHost on your Apache web server
- Uncompress the website on this new vHost folder : pwddb
- Uncompress the sql script to create the database structure : db_create
- You can use phpMyAdmin to execute the database creation script
Configuration
- Open and configure the file config.ini
- Open and update the file @.security to insert the Distinguished Name of the groups that will be authorized to login to the password Database
If you have any problems, contact me or leave a comment !
Thank you to
References
adLDAP – LDAP Authentication with PHP for Active Directory
adLDAP is a PHP class that provides LDAP authentication and integration with Active Directory.
Intelligent Active Directory integration with PHP was a holy grail for most intranet developers for a long time. This project is really to help others with getting over the same hurdles that we’ve experienced in getting the whole LDAP SSL Active Directory puzzle working natively on Linux.
Given the varied nature of organisations and sites, adLDAP may not be _your_ complete solution, but it should be a very sound starting point. LDAP isn’t overly friendly on first glance, and it’s a steep learning curve made alot worse when coupled with Microsoft’s seemingly unending army of gotcha’s.
The information you can retrieve from Active Directory is as useful as you make it. If you don’t fill out all their account information there’s not really going to be much to query.
My Powershell script categories
- Active Directory
- Cluster
- Database
- Exchange
- Files and folders
- Hardware
- Network
- Operating System
- PKI
- SCCM
- Service and process
- Tips
- VMWare

Can we get some more clarification on what each line of the config file and security file should be changed to?
Hello Keith,
Really sorry for this late answer. The config.ini file is the following :
host = “localhost”
user = “dbuser”
pass = “dbpwd”
passphrase = “l5uJKTxgxE5MPTKv2m3w7q316M0”;
databaseName = “pwd_db”;
tableName = “pwd_table”;
tableHistory = “history”;
accountSuffix = “@domain.local.net”
baseDn = “DC=domain,DC=local,DC=net”
domainControllers = “domain.local.net”
pwdsection[] = “AD”
pwdsection[] = “Applications”
pwdsection[] = “Exchange”
pwdsection[] = “Network”
pwdsection[] = “Firewall”
pwdsection[] = “Others”
pwdsection[] = “Antivirus”
pwdsection[] = “Database”
pwdsection[] = “FTP”
pwdsection[] = “Monitoring”
pwdsection[] = “Web”
pwdsection[] = “Storage”
The “host” variable is the name or IP address of the database server.
“user” and “pass” variables are the credentials to interact with the database (read/write)
The “passphrase” variable is used to encrypt the data in the database. Use your own passphrase with alphanumeric characters.
database, tablename, tablehistory variables don’t have to be changed if you use the mysql script in this article to create your database
accountSuffix, baseDn and domaincontrollers have to be updated with your own parameters according to your active directory environment. domaincontrollers variable contains the domain name. With this setting, one of the dc will be requested for LDAP instead of define each dc names.
the pwdsection[] are free and set in the config.ini with examples. You can add, remove or change these lines as you want/need.
Hope my comments help you.
Regards
Nico