
If you used the application Passwords for Owncloud to store your credentials, you have seen recently this app does not exist anymore. The application has been removed from Github and it is hard to find the documentation. This is why I have worked on the migration from the Passwords application to Passman.
Passman is a full featured password manager.
Features:
– Vaults
– Vault key is never sent to the server
– Credentials are stored with 256 bit AES
– Ability to add custom fields to credentials
– Built-in OTP (One Time Password) generator
– Password analyzer
– Share passwords internally and via link in a secure manner.
– Import from various password managers (KeePass, LastPass, DashLane, ZOHO, Clipperz.is )For an demo of this app visit https://demo.passman.cc
First of all, you will have to backup your current passwords stored in the Owncloud database. Follow these steps:
Get the following variables stored in the Owncloud configuration file (by default, /var/www/owncloud/config/config.php ) :
... 'dbname' => 'owncloudDBName', 'dbuser' => 'owncloudDBuser', ...
After that, you can export the Passwords application table :
mysql -u owncloudDBuser -p -e "use owncloudDBName; select website,pass,properties,notes from oc_passwords where deleted=0" -B | sed "s/'/\'/;s/\t/\",\"/g;s/^/\"/;s/$/\"/;s/\n//g" > mytable.csv
I have written the following php page to decrypt the informations stored in the csv file exported above :
<?php
function pbkdf2($algo, $key, $salt, $rounds, $length) {
$size = strlen(hash($algo, '', true));
$len = ceil($length / $size);
$result = '';
for ($i = 1; $i <= $len; $i++) {
$tmp = hash_hmac($algo, $salt . pack('N', $i), $key, true);
$res = $tmp;
for ($j = 1; $j < $rounds; $j++) {
$tmp = hash_hmac($algo, $tmp, $key, true);
$res ^= $tmp;
}
$result .= $res;
}
return substr($result, 0, $length);
}
function getKeys($salt, $key) {
$ivSize = mcrypt_get_iv_size(MCRYPT_BLOWFISH, MCRYPT_MODE_CBC);
$keySize = mcrypt_get_key_size(MCRYPT_BLOWFISH, MCRYPT_MODE_CBC);
$length = 2 * $keySize + $ivSize;
$rounds = 100;
$key = pbkdf2('sha512', $key, $salt, $rounds, $length);
$cipherKey = substr($key, 0, $keySize);
$macKey = substr($key, $keySize, $keySize);
$iv = substr($key, 2 * $keySize);
return array($cipherKey, $macKey, $iv);
}
function makeKey($userKey, $serverKey, $userSuppliedKey) {
$key = hash_hmac('sha512', $userKey, $serverKey);
$key = hash_hmac('sha512', $key, $userSuppliedKey);
return $key;
}
function unpad($data) {
$length = mcrypt_get_block_size(MCRYPT_BLOWFISH, MCRYPT_MODE_CBC);
$last = ord($data[strlen($data) - 1]);
if ($last > $length) return false;
if (substr($data, -1 * $last) !== str_repeat(chr($last), $last)) {
return false;
}
return substr($data, 0, -1 * $last);
}
function decrypt($data_hex, $key) {
if ( !function_exists( 'hex2bin' ) ) {
function hex2bin( $str ) {
$sbin = "";
$len = strlen( $str );
for ( $i = 0; $i < $len; $i += 2 ) {
$sbin .= pack( "H*", substr( $str, $i, 2 ) );
}
return $sbin;
}
}
$data = hex2bin($data_hex);
$salt = substr($data, 0, 128);
$enc = substr($data, 128, -64);
$mac = substr($data, -64);
list ($cipherKey, $macKey, $iv) = getKeys($salt, $key);
$dec = mcrypt_decrypt(MCRYPT_BLOWFISH, $cipherKey, $enc, MCRYPT_MODE_CBC, $iv);
$data = unpad($dec);
return $data;
}
function cryptoJsAesDecrypt($jsonString,$webs){
# this is the variable 'passwordsalt' that can be found in /var/www/owncloud/config/config.php
$serverKey='xxxxxxxxxxxxxxxxxxxxxx+yyyyy';
# this variable is the Owncloud username where the Passwords vault has been created
$userKey='owncloudusername';
$userSuppliedKey=$webs;
$key=makeKey($userKey, $serverKey, $userSuppliedKey);
$last=decrypt($jsonString, $key);
$sendButton = "done";
return $last;
}
$csv = array_map('str_getcsv', file('mytable.csv'));
array_walk($csv, function(&$a) use ($csv) {
$a = array_combine($csv[0], $a);
});
array_shift($csv); # remove column header
echo '"title","password","username","url","notes"';
foreach($csv as $tag){
$ws = $tag['website'];
$ps = $tag['pass'];
$pp = $tag['properties'];
$rs = cryptoJsAesDecrypt($ps,$ws);
$rp = cryptoJsAesDecrypt($pp,$ws);
echo "
\"".$ws."\",\"".$rs."\",";
$desc_arr = explode(",", $rp);
echo (explode(" : ",$desc_arr[0])[1]).",";
echo (explode(" : ",$desc_arr[1])[1]).",";
preg_match_all('/"(?:\\\\.|[^\\\\"])*"|\ :\ /', $rp, $matches);
echo preg_replace("/\,/","",$matches[0][32]);
}
?>
It is important to customize the lines in the php file above with your own values (lines 79 and 82) in the function cryptoJsAesDecrypt :
# this is the variable 'passwordsalt' that can be found in /var/www/owncloud/config/config.php
$serverKey='xxxxxxxxxxxxxxxxxxxxxx+yyyyy';
# this variable is the Owncloud username where the Passwords vault has been created
$userKey='owncloudusername';
Open the php page with your favorite web browser and your passwords will be shown decrypted. It is now possible to simple copy the content of the page in a file and then import it into Passman.
Open Passman application and click on Settings
Click on the link called Settings
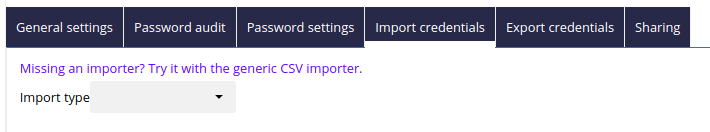
Go to the import credentials tab and click on the link “Missing an importer?…”
Click on the button “Choose File” and select the decrypted file copied previously from the php page
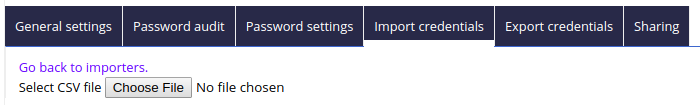
Check everything seems correct and click on the button “Start import”
You have now all your passwords migrated to Passman !
Do not hesitate to contact me if you have any questions on implementing this procedure.
My Powershell script categories
- Active Directory
- Cluster
- Database
- Exchange
- Files and folders
- Hardware
- Network
- Operating System
- PKI
- SCCM
- Service and process
- Tips
- VMWare
